Electron Diffraction – Related STAIB Instruments Products

What is RHEED?
Principle:
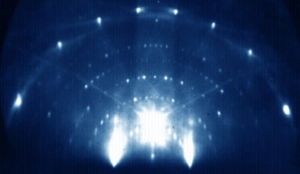
Electrons can be diffracted by a surface in a similar way as visible light, except that the associated wavelength is much smaller. Low energy electrons have a wavelength that is in the order of atomic spacing and can be diffracted by lattice atoms. High energy electrons have a wavelength much smaller than the lattice spacing and diffraction conditions can be reached simply by setting the incident beam at a very small incidence angle to the surface. The diffracted electrons build a diagram consisting of a superposition of spots at Bragg angles for the bulk material, streaks from the surface diffraction, and Kikuchi lines from channeling effects.
The ability to monitor variations of the diagram during deposition is most valuable. RHEED delivers real time detailed information about the crystal structure of the bulk and the smoothness and crystalline quality of the surface layer with a sub-monolayer resolution. When used in a deposition device, the diffraction diagram instantly displays the surface modifications. The intensity of diffraction spots or streaks is used to monitor the deposition at a layer-by-layer sensitivity (technique named RHEED oscillations).
RHEED is the premium choice technique for growth monitoring since multiple different parameters can be captured simultaneousley in situ, and in real time.
Technique:
In order to produce sharp diffraction spots, the high energy primary RHEED beam (typically above 10 keV) must be of small size, and highly collimated. Electron guns for RHEED fulfill these requirements using suitable electron optical lenses, which allow full electronic control of the beam parameters. The electron gun is mounted at grazing incidence angle towards the sample surface. The diffracted electrons are imaged on a fluorescent screen mounted on the opposite side of the sample. The screen can be protected with a shutter when not in use. The diffraction diagram displayed is digitalized using a CCD camera.
The video feed can be analyzed in a suitable RHEED acquisition software. Here, the area of interest can be set on the RHEED diagram to follow the signal intensity variations, which can be instantly converted into growth rate and layer thickness.
Setup:
The standard setup requires an electron gun suitable for RHEED with an energy in the range of 10 to 60 keV. The electron gun is mounted onto the vacuum chamber to achieve a glazing incidence angle to the surface. The angle to the surface should be adjustablein in the range of 1 to 3 degrees. Previously, this has been done using precise mechanical orienters. Today state-of-the-art uses a very precise electronic beam rocking control (STAIB Beam Rocking and STAIB Advanced Beam Steering). The distance between gun and sample can be quite large to allow full clearance around the sample. The multilayer fluorescent screen includes a special phosphorous deposited on lead glass (to block X-rays generated in the chamber). It is designed to enhance contrast by blocking light and low energy electrons from inside the chamber. A shutter can be used to protect the screen and extend its lifetime.
The acquisition and digitalization of the diffraction diagrams is performed by a low noise CCD camera with selectable sensitivity and speed. Changes of the crystal structure, the number of layers deposited, and the deposition rate can be measured during the process simultaneousley.
Useful options:
- Beam rocking capability to electronically fine adjust the incidence angle.
- A high beam energy option for operation of RHEED in large vessels, or in order to work with poorly diffracting samples (high energy allows more bulk diffraction) and samples with poor and complex crystal structures (such as textures, nanofibers). High energy guns of 100 keV are also used for gas diffraction.
- Addition of pumping stage (differential pumping) to the electron gun allows it to work under poor vacuum conditions (TorrRHEEDTM), a common requirement for many deposition systems, such as PLD, IBD, MOMBE and more.
- Blanking the electron beam (beam blanking) allows fast control of the beam (switching on/off) that can be used for rotating samples and to drastically reduce the electron impact effects on electron sensitive surfaces (organic materials).
SEY (Secondary Electron Yield), SED (Secondary Electron Distribution), and Backscattered Electron Yield
